The Ultimate Online Course for Mastering WiFi & Wireless Penetration Testing
Land a high-paying cybersecurity role without spending years in expensive degree programs.
Capture, Crack, and Secure WiFi Networks Like a Certified Pro!
CLICK BELOW TO WATCH FIRST!

4.9/5 star reviews
Hundreds of happy customers worldwide
AS SEEN ON



Discover Why Wireless Security Skills Are Critical for Your Cybersecurity Career
Does this sound like you?
Unsure which adapters, antennas, and tools actually work in the real world.
Struggling to capture reliable handshakes or crack modern passwords.
Lacking a safe lab to practice without risking legal trouble.
Unable to pivot from WiFi to internal networks during audits.
No idea how to write reports that land jobs or consulting clients.
Follow our proven methodology for scoping, exploiting, and securing any wireless network.
Master industry-standard tools like Aircrack-ng, Hashcat, Wireshark, and Kismet.
Use our downloadable virtual lab and sample handshakes to practice 24/7.
Invest only in instructor-vetted adapters and antennas that work flawlessly with Kali Linux.
Create executive-level reports that win jobs, promotions, and freelance contracts.
What You Receive Inside Wireless Mastery

Wireless Fundamentals & Gear
Grasp WiFi architecture, standards, and the must-have adapters, antennas, and radios.

Lab Setup & Tool Installation
Build an isolated lab, install Kali Linux, and configure the Aircrack-ng suite and Wireshark.

Packet Capture & Analysis
Sniff packets, perform deauth attacks, and capture WPA/WPA2 handshakes like a hunter.

WPA/WPA2 Cracking Mastery
Crack pre-shared keys, extract PMKID hashes, and unleash GPU power with Hashcat.

Rogue APs & Evil-Twin Attacks
Deploy Evil-Twin access points, DNS spoofing, and captive portals to harvest credentials.

Client-Side Wireless Exploitation
Execute KARMA and LLMNR attacks, inject payloads, and phish users over wireless.
TESTIMONIALS
What our students are saying...

"Highly recommended course. The instructor has in-depth knowledge of wireless pentesting methods and extensive experience with real-world projects. The course covers everything from the basics to advanced wireless exploitation techniques. Absolutely worth every penny!!!!"
- Kyaw Min Thein


"As I was thinking I know about Wireless security, there came Toby Reynolds to tell me you got to learn more. The content was way very good, and the way the live cohort went with all the tools installed on the VM and doing hands-on was amazing. Worth the money, considering you will have access to Toby Reynolds himself all the time, any live cohort and live time update to the course. This course is nothing short of amazing again. This is evolving. I highly recommend."
- Abhishek Narasimhan


"Just wrapped up the WIFI Novice to professional course with TheXero Training — and I have to say Toby Reynolds provided insightful and practical training experiences I’ve had in a long time. From real-world WiFi design and deep dives into security, simple, clear explanation of WiFi fundamentals, and live lab setups, this course doesn’t just teach you how things work — it helps you understand why they work. The hands-on sessions made complex networking concepts come alive, and Toby's explanations approach truly sharpened the way I think about wireless architecture, rather than just memorizing steps or commands. Some awesome training to end the weekend and a powerful quote to keep on learning."
- Jag Singh

MODULES
FOLLOW MY STEP BY STEP VIDEO TRAINING
Wireless Fundamentals & Gear
Grasp WiFi architecture, standards, and the must-have adapters, antennas, and radios.

Lab Setup & Tool Installation
Build an isolated lab, install Kali Linux, and configure the Aircrack-ng suite and Wireshark.
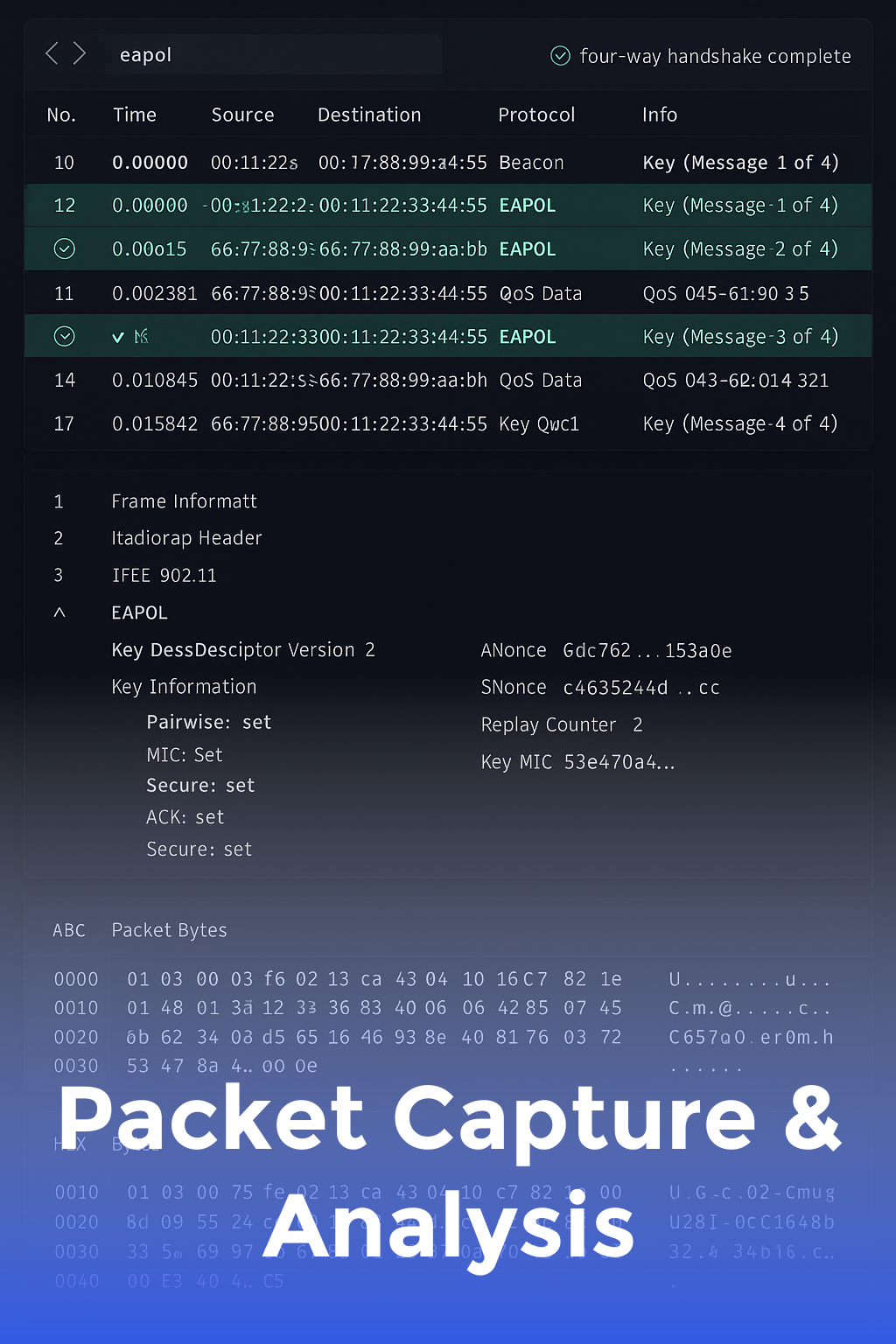
Packet Capture & Analysis
Sniff packets, perform deauth attacks, and capture WPA/WPA2 handshakes like a hunter.
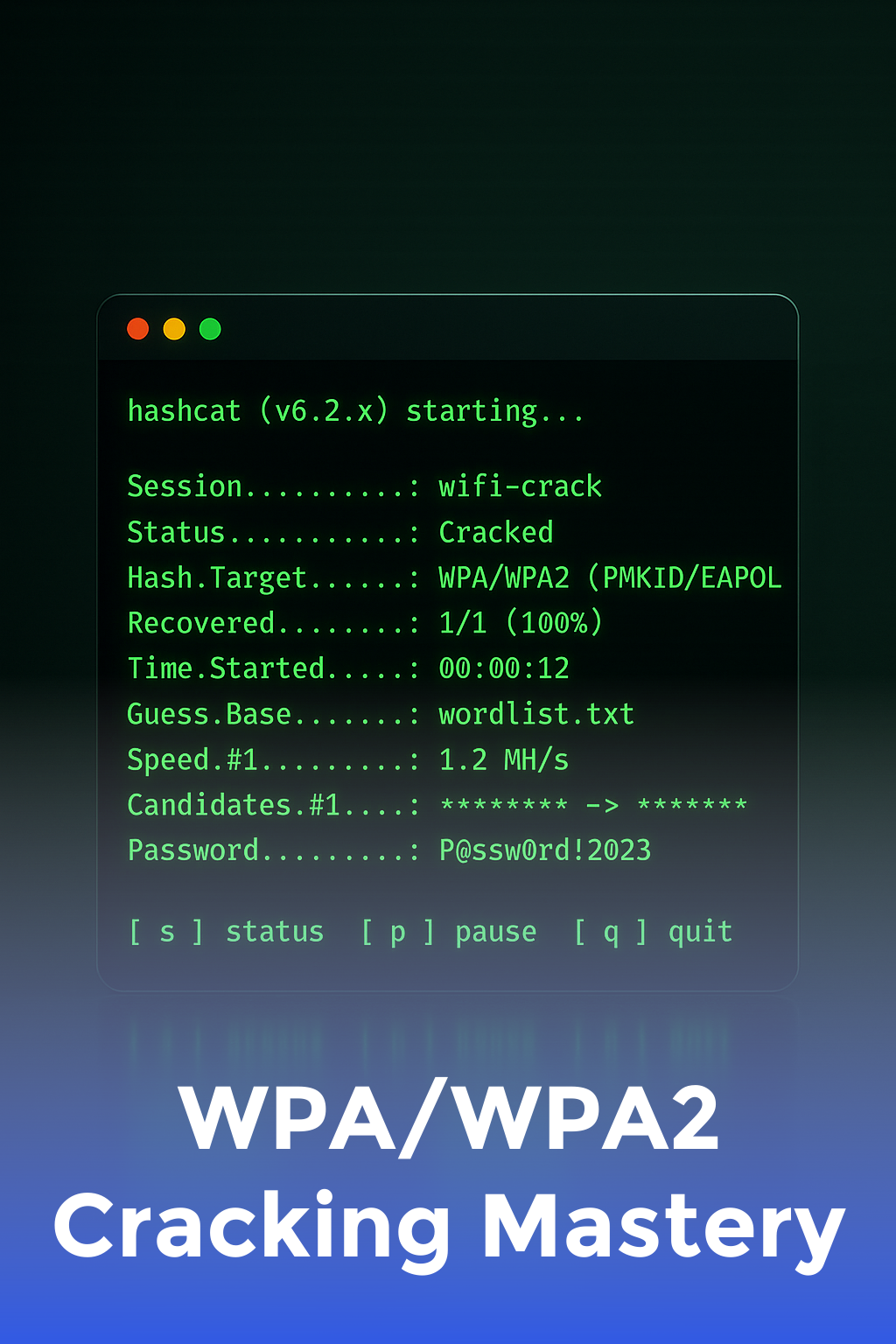
WPA/WPA2 Cracking Mastery
Crack pre-shared keys, extract PMKID hashes, and unleash GPU power with Hashcat.

Rogue APs & Evil-Twin Attacks
Deploy Evil-Twin access points, DNS spoofing, and captive portals to harvest credentials.
Client-Side Wireless Exploitation
Execute KARMA and LLMNR attacks, inject payloads, and phish users over wireless.
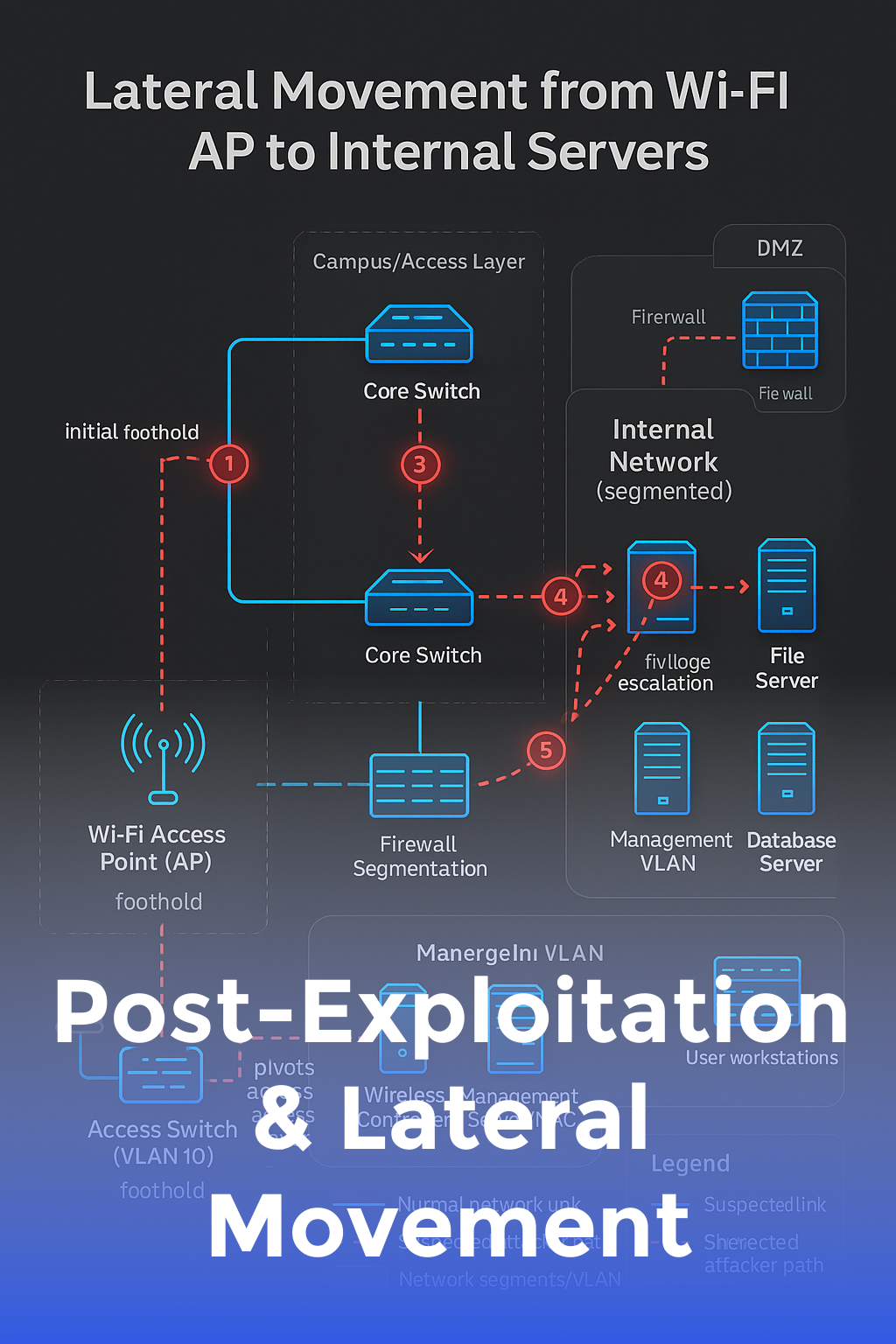
Post-Exploitation & Lateral Movement
Pivot from wireless foothold to internal networks using Metasploit tunneling & SOCKS proxies.

Reporting & Hardening Best Practices
Write professional pentest reports and implement defenses like WPA3, 802.1X, and WIDS.

4.9/5 star reviews
Become a Professional WiFi & Wireless Pen-Testing Specialist
Learn the exact tools, tactics, and methodologies used by security experts to attack and secure wireless networks with our hands-on, step-by-step video program.
Here's what you get:
Instant streaming access to HD, closed-captioned lessons.
Downloadable lab guide, custom scripts, and exclusive discount links for adapters.
Membership in a private Discord community of wireless hackers.
Lifetime course updates covering WPA3, WiFi 7, and emerging standards at no extra cost.
Personal mentorship and accountability to ensure that your goals are met.
Today Just
$599 one time

"Best purchase ever!"
" As a network admin, I finally understand how attackers target our WiFi. I plugged six critical holes the first week. "
ABOUT YOUR INSTRUCTOR
Meet Toby
Taught by a certified Offensive Security Wireless Professional (OSWP) and former Fortune 500 security engineer with 12+ years of experience breaking and defending WiFi networks worldwide.
After seeing countless companies overlook wireless threats, he realized new talent needed structured, lab-driven guidance. He built this course so students can confidently audit and secure any WiFi network from day one.
Graduates now work at companies like Cisco, CrowdStrike, and Deloitte. Many report 30–50% salary increases after adding proven wireless skills to their résumés.
Wireless penetration testing services lead for a global security consultancy accessing thousands of networks per year.
Active contributer and speaker at OWASP, Christchurch Con, and BSides London.
Helped hundreds of students break into offensive security penetration-testing roles.
Discovered and responsibly disclosed vulnerabilities to top hardware vendors.

WHO IS THIS FOR...
Perfect for ethical hackers, network administrators, security analysts, and aspiring cybersecurity professionals who want to dominate wireless testing and land high-paying jobs.
Ethical Hackers & Pentesters
Network & System Administrators
Cybersecurity Students Preparing for OSWP/CEH
IT Professionals Transitioning to Security
Freelance Security Consultants
Bug Bounty Hunters Targeting IoT
Wireless Engineers & Architects
Tech Enthusiasts Who Love Hands-On Labs
STILL NOT SURE?
Satisfaction guaranteed
We want you to find value in our trainings! We offer full refunds within 30 days. With all of our valuable video training, we are confident you WILL love it!

STILL GOT QUESTIONS?
Frequently Asked Questions
Do I need prior hacking experience?
Basic networking knowledge is helpful, but we start from the ground up. You’ll build skills progressively until you’re ready for advanced WiFi attacks.
Is the course legal and ethical?
Yes! All content is taught under an ethical hacking framework. You’ll practice in isolated labs and learn how to gain written authorization before testing production networks.
How is this course different from YouTube tutorials?
Wireless Mastery offers structured, lab-driven progression, real-world reporting templates, instructor feedback, and a supportive community—none of which free videos provide.
Enroll in the course now!
Copyrights 2026 | Wireless Mastery™ | Terms & Conditions
